Cellframe Network Hack Analysis
Cellframe Network Hack Analysis
Overview:
On June 1, 2023, Cellframe Network suffered a security breach caused by a vulnerability that arose due to calculation issues with token quantities during the liquidity migration process, leading to a loss of 76,112 USD.
Smart Contract Hack Overview:
- Attackers address: 0x2525c8
- Attack contract: 0x1e2a25
- Address OLD_CELL: 0xf3e144
- Address LP_OLD:0x06155
- Address CELL: 0xd9843
- Address LP_NEW: 0x1c15f4
- Pre-Attack Transaction: 0xe2d496
- Attack Transaction:0x943c2a
Decoding the Smart Contract Vulnerability:
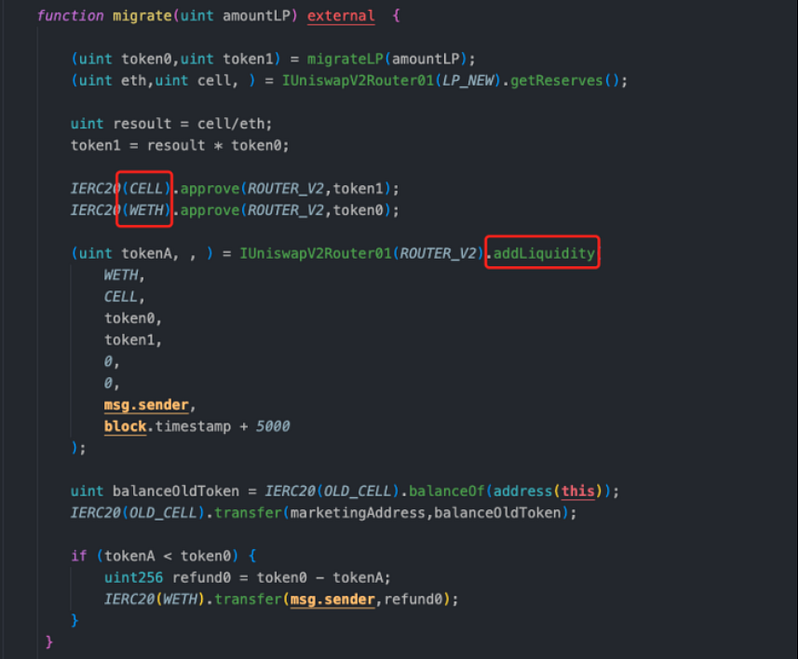
- The root cause of the vulnerability was identified as calculation issues with token quantities during liquidity migration.
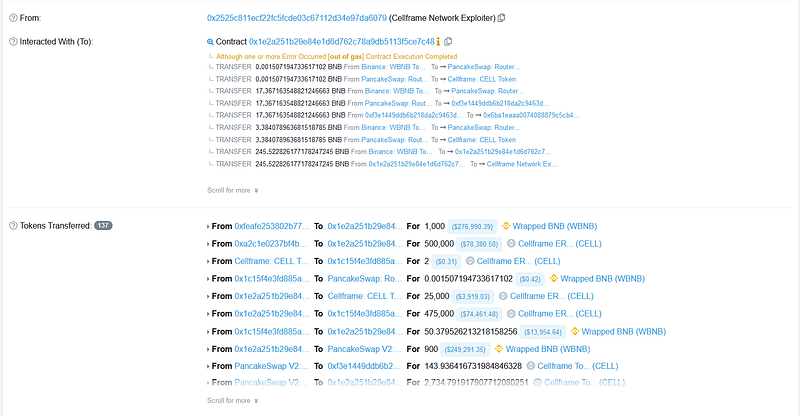
- The attacker started the attack by taking a flash loan from DPP and acquiring 1,000 BNB. They then leveraged another flash loan from Pancake V3 to obtain 500,000 “new cell” tokens.
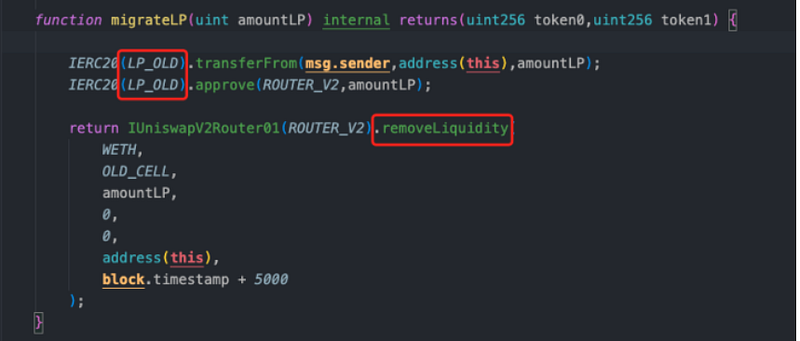
- After converting all of the “new cell” tokens into BNB, the BNB balance in the pool significantly diminished, almost reaching zero. Taking advantage of this situation, the attacker used 900 BNB to acquire “old cell” tokens. They further enhanced the liquidity by adding both “old cell” and BNB, which enabled them to obtain “old LP” tokens.
- The attacker triggered the liquidity migration process, where the new pool had very little BNB, and the old pool had a limited supply of “old cell” tokens. As part of the migration, removing liquidity resulted in a rise in BNB and a reduction in “old cell” tokens due to their scarcity in the old pool.
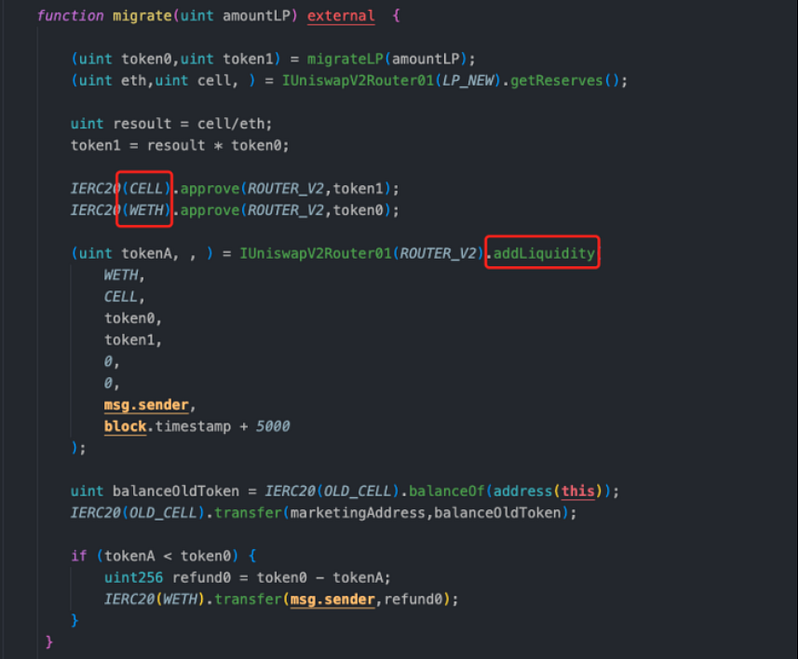
- The variables
resoultandtoken1increased. Users needed only a small quantity of BNB and “new cell” tokens to acquire liquidity. Any surplus BNB and “old cell” tokens were given back to the users. - The process of liquidity migration was repeated several times, taking advantage of the imbalanced condition of the pools and increasing the gains for the attacker. Each iteration further exploited these imbalances. It highlights the vulnerabilities that emerge when token quantities are not sufficiently taken into account.
- The attacker removed liquidity from the new pool and exchanged the returned “old cell” tokens for BNB. As a result, the old pool accumulated a significant number of “old cell” tokens but had no BNB left. Subsequently, the attacker effectively converted the “old cell” tokens back into BNB earning a profit of ~245.52 BNB.
Mitigation and Best Practices:
- Ensure that the token calculation is done properly keeping in mind the external factors.
- Thoroughly test the contract’s functionality under various scenarios and edge cases to identify and address potential logic flaws or vulnerabilities. Write test cases for each possible scenario.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
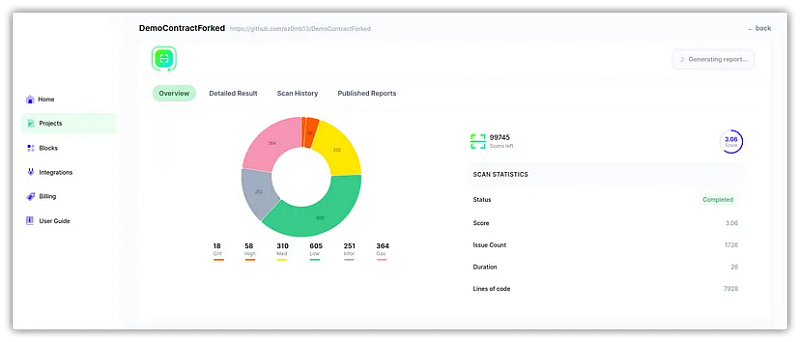
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan
Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
New to trading? Try crypto trading bots or copy trading on the best crypto exchanges
Also Read
- Copy Trading | Crypto Tax Software
- CoinTracking Review | Koinly Review
- Grid Trading | Crypto Hardware Wallet
- Crypto Telegram Signals | Crypto Trading Bot
- Best Crypto Exchange | Best Crypto Exchange in India
- Best Crypto APIs for Developers
- Best Crypto Investing Apps
- TOP 6 Play to Earn Crypto Games
- Best Crypto Lending Platform
- Top 8 Crypto Jewelry
- Free Crypto Signals | Crypto Trading Bots
- An ultimate guide to Leveraged Token
- NFT Trading Signals
Join Coinmonks Telegram Channel and Youtube Channel to get daily Crypto News
