BRA Token Hack Analysis — Double the Reward
BRA Token Hack Analysis — Double the Reward
Overview:
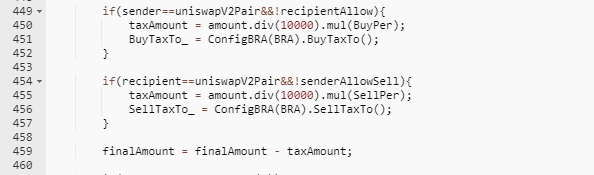
- Another hack occurred on January 10, 2023, when the BRA token was attacked, allowing the hacker to steal funds worth 819 WBNB, or approximately $225,000. The primary cause was a logical vulnerability that let the attacker invoke the transfer function, which resulted in twice the rewards if the sender and recipient were a pair.
Smart Contract Hack Overview:
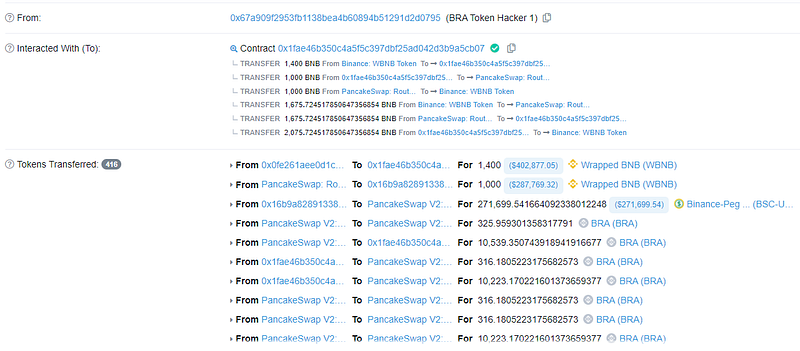
- Attacker’s Transaction: 0x6759db55
- Attacker’s Address: 0x67a909f295, 0xE2Ba15be
- Attacker’s Wallet pending funds: 0x67a909f2953fb
- BRA Token Code: 0x449fea37
- Pancake Swap Contract: 0x8f4ba1832
Decoding the Smart Contract Vulnerability:
- Attackers obtained a 1,400 WBNB flash loan before exchanging 1,000 WBNB for 10.5K BRA tokens and transferring all acquired BRA tokens to the Pancakeswap pair.
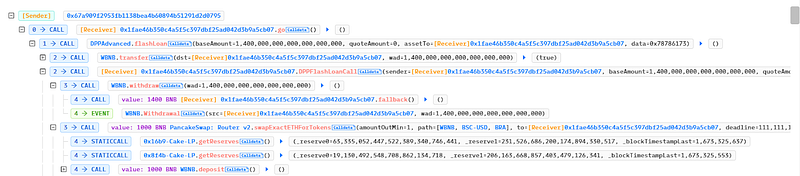
- Attackers then used the skim() function and invoked the BRA contract’s transfer function to receive rewards.
- “
skim()” acts as a recovery mechanism if the number of tokens supplied to a pair exceeds the two uint112 storage spaces for reserves (reference).
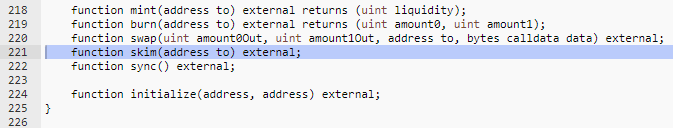
- In the above case, the attacker provided pair as the recipient address, and BRA reverted to the pair, resulting in a BRA amount being doubled after a single skim. The same method was performed 100 times, and the contract pair’s BRA balance significantly increased.
- The attacker then returned 1.675K WBNB tokens and repaid the 1.4K WBNB token flash loan which generated a profit of 675 WBNB which was sent to their address.

- The attacker again carried out this same attack and took 144 WBNB in profit from the BRA contract.
Mitigation and best practices:
- Proper validations must be done on the key-pair inputted by the users and if any case can exploit a functionality, then it should not be allowed to be passed into the contract and should be validated using require or assert conditions.
- It’s recommended to validate all users’ input and use modifiers on critical functionalities that may affect the bool balances and users’ funds.
- The mathematical logic should be thoroughly tested and validated so that it doesn’t lead to false results affecting the entire contract.
- Conduct thorough testing and reviews of the smart contract code to identify and fix any potential vulnerabilities before deployment.
- Use established contract patterns, such as the Open Zeppelin library, which has been audited and tested for security vulnerabilities.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
