BonqDAO Protocol Hack analysis — Oracle Manipulation
BonqDAO Protocol Hack analysis — Oracle Manipulation
Overview:
On February 1st, 2023, another oracle manipulation attack took place, costing the BonqDAO protocol $120 million. By using an oracle manipulation technique, the attackers completely altered the price of AllianceBlock’s $ALBT tokens, yielding them huge profits.
Smart Contract Hack Overview:
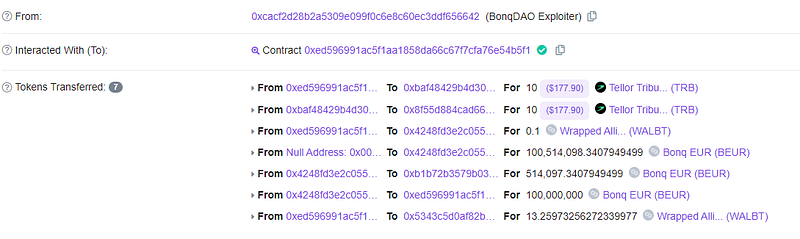
- Attacker’s transaction: 0x31957ecc
- Attacker’s address: 0xcacf2d2
- BonqDAO exploiter’s contract: 0xed5969
- TellorFlex Contract code: 0x8f55D884C
- BonqDAO Smart Contract: 0x4248fd3e2
- BonqProxy Contract: 0xb1b72b3
Decoding Smart Contract Vulnerability:
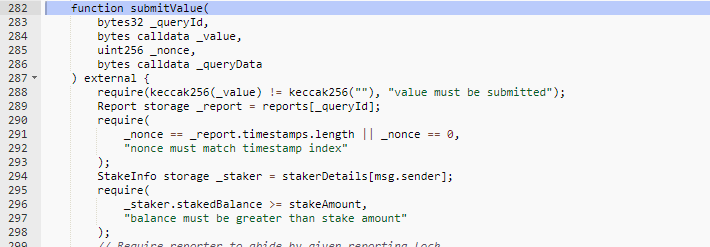
1. The Tellor protocol, a decentralized and permissionless data reporting off-chain oracle that on-chain contracts can consume, was utilized by BonqDAO, a collateralized lending platform.
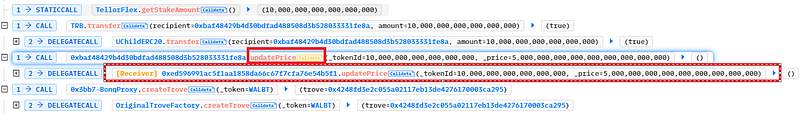
2. Before reporting any value as a token price, the Tellor protocol needed 10 TRB tokens to be staked. The attacker entered the teller oracle as a reporter after staking 10 TRB tokens.
3. The attacker set the price of WALBT to be extremely high value (5e27).
4. Any WALBT token on the Bonq & Tellor protocol was worth billions of dollars as the price went up.
5. Since the Tellor Protocol contained a mechanism to slash or remove a reporter’s staked TRB tokens if the price reported was inaccurate, the price was adjusted to normal on Tellor’s Oracle.
6. Following the attacker’s price manipulation, they minted $100 million worth of BEUR tokens and exchanged them for their USDC counterparts via Uniswap.
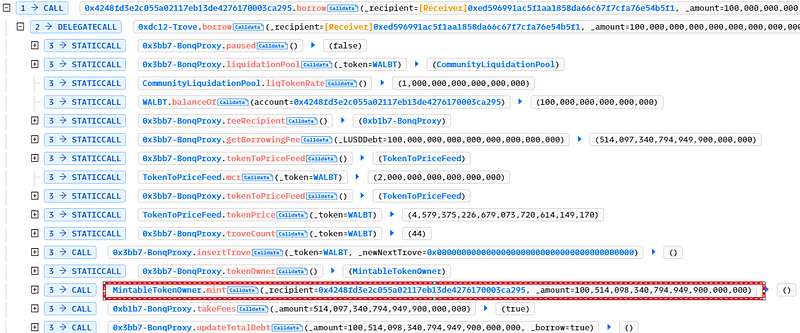
7. The BonQ protocol was unable to handle the change made in the Tellor oracle price in a single transaction, which allowed the instant price to be consumed for the WALBT token, causing a loss of over 120M.
Mitigation and Best Practices:
- The protocol using oracle as price feeds must have a time difference in order for the price to be checked and verified before being utilized, and it cannot significantly rely on changes made in the oracle instantly.
- Protocols need to add security layers, using at least two oracles to verify the price. This would mitigate the hack and ensure proper checks on critical functions and variables that are publicly accessible.
- Price manipulation attempts can be mitigated to a greater extent via oracles such as Chain Links and input validation on those feed parameters to prevent stale data.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ patterns at SolidityScan

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
