Bitkeep Hack Analysis — Unofficial app Hijacked
Bitkeep Hack Analysis — Unofficial app Hijacked
Overview:
- The BitKeep cryptocurrency wallet’s APK version 7.2.9 was cloned by attackers in a phishing scandal, and $8 million in user funds were stolen, it was announced at the end of December 2022.
Smart contract hack overview:
- Malicious APKv: 7.2.9
- Attack Vector: Malicious BitKeeps Apk was hosted on several fraudulent websites.
Decoding the Vulnerability:
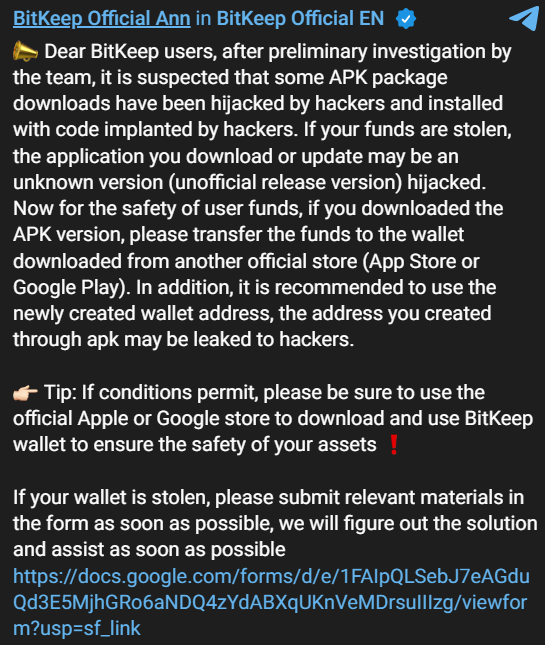
- Bitkeep officials discovered its users complaining about crypto wallets that do not require validation being emptied. Following an internal investigation, it was discovered that attackers hijacked unofficial versions of the Bitkeep Android app that had not yet been publicly published.
- The attackers were able to alter the functionality of the program to include malicious code due to access to these APK files.
- Unknown to the victims, the APK file they downloaded from the website contained malicious code intended to steal the seed phrases of naive users.
- After installing the original applications from Google Play or the App Store, those who downloaded the trojanized APK package are recommended to move all funds to the official store, create a new wallet address, and transfer all cash.
- Any wallet addresses produced by the malicious APK should be regarded as compromised, the platform advised.
Mitigation and best practices:
- The attack highlights how crucial it is for cryptocurrency users to follow appropriate security procedures and to be aware of legitimate apps available and websites to avoid falling victim to such fraud.
- Only ever download the most recent official Crytpo apps from the Google Play Store or App Store.
- Always verify the legitimacy of websites and applications before entering sensitive data, including passwords, private keys, and seeds, as they are crucial for maintaining crypto security.
- To prevent hackers, always have your app’s source code obfuscated along with binary hardening methods, and do regular penetration tests on Android applications, especially the ones handling user data and funds.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
