BankXio Hack Analysis
BankXio Hack Analysis
Overview:
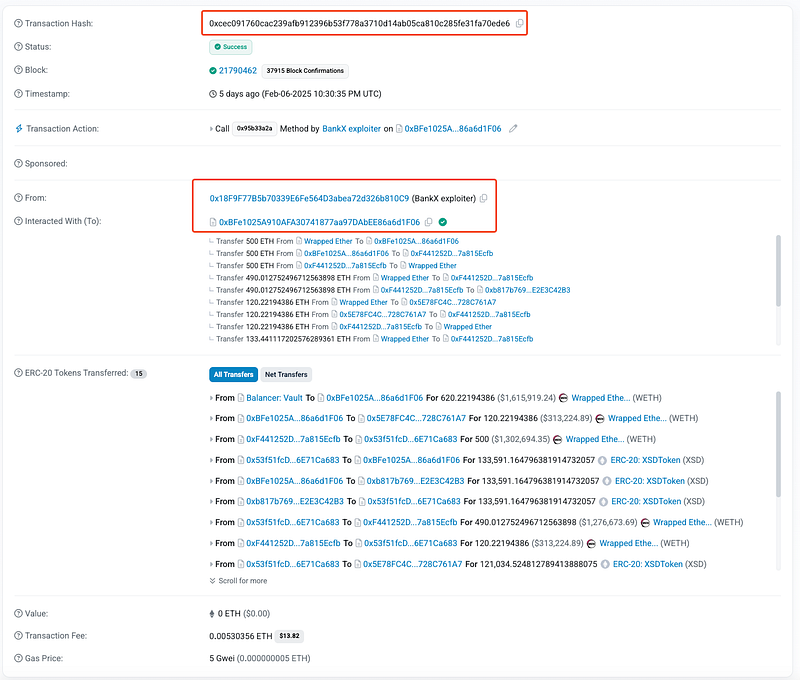
On February 8, 2025, BankX (@BankXio), operating on BSC, Ethereum, and Optimism, suffered a reentrancy attack that resulted in a loss of approximately $43,000. The exploit targeted the swapXSDForETH function within the Router contract, allowing the attacker to manipulate token burns due to an incorrect pool state during swaps.
Smart Contract Hack Overview:
Decoding the Smart Contract Vulnerability:
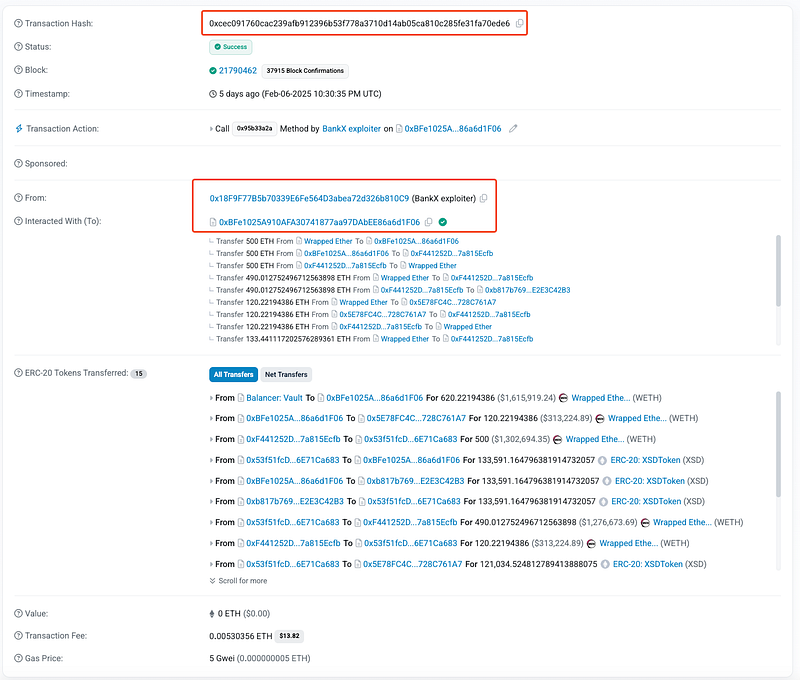
- The root cause of the exploit lies in the incorrect state validation and lack of reentrancy protection in the
swapXSDForETHfunction. Specifically, the contract fails to properly update pool states before executing the burn operation, allowing the attacker to repeatedly burn XSD tokens beyond the expected limits.
- The attacker triggered a swap, sending XSD tokens to the pool and receiving ETH in return. The
swapXSDForETHfunction executesIXSDWETHpool(XSDWETH_pool_address).swap(0, amountOut, address(this)), leading to an external call before state updates. - Before state changes were finalized, the attacker repeatedly invoked the function. Due to improper state validation, the
burnpoolXSDfunction is triggered multiple times, burning more XSD than expected. - Then attacker called
IWBNB(WETH).withdraw(amountOut);to unwrap WETH to ETH. The ETH is transferred to the attacker’s wallet viaTransferHelper.safeTransferETH(msg.sender, amountOut);.
Mitigation and Best Practices:
- Implement
nonReentrantmodifiers to prevent reentrant calls in theswapXSDForETHfunction. - Update internal balances before performing any external transfers to prevent stale state exploitation. Also, ensure pool reserves are dynamically checked after swaps to prevent outdated reserve usage.
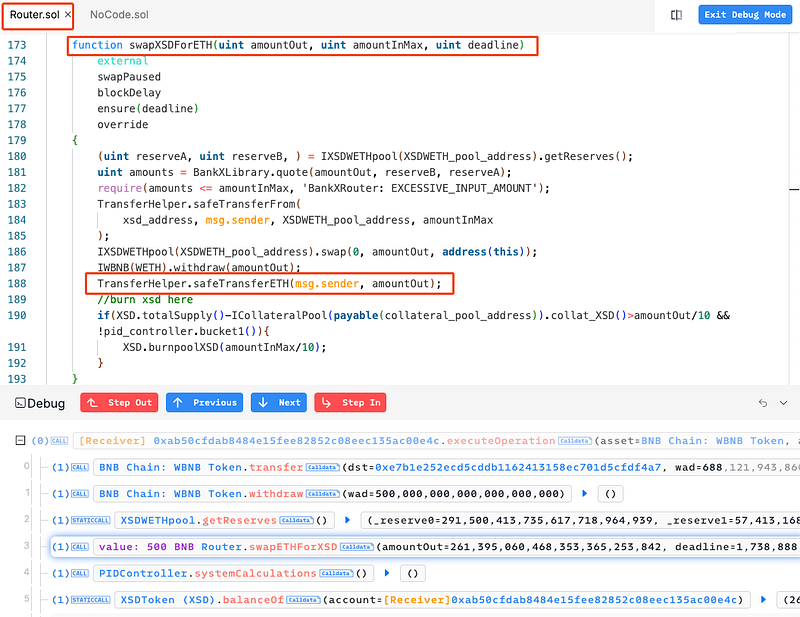
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
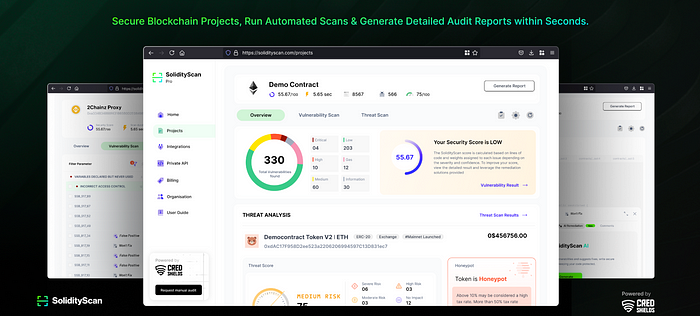
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
