Astrid Finance Hack Analysis
Astrid Finance Hack Analysis
Overview:
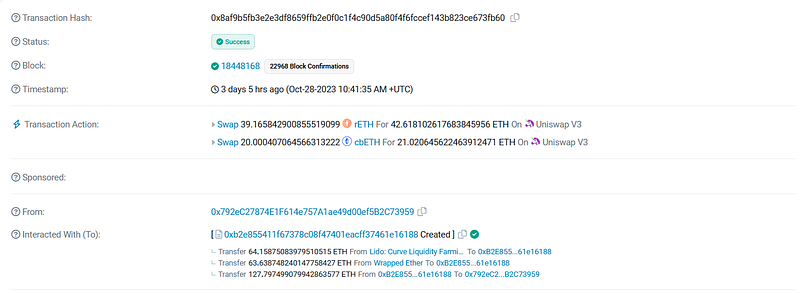
On October 28, 2023, Astrid Finance suffered an attack due to a business logic vulnerability, leading to an approximate loss of ~127ETH.
Smart Contract Hack Overview:
- Attacker address: 0x792ec2
- Attack Contract:0xb2e855
- Vulnerable Contract:0xbAa875
- Attack Transaction: 0x8af9b5
Decoding the Smart Contract Vulnerability:
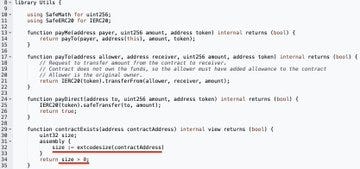
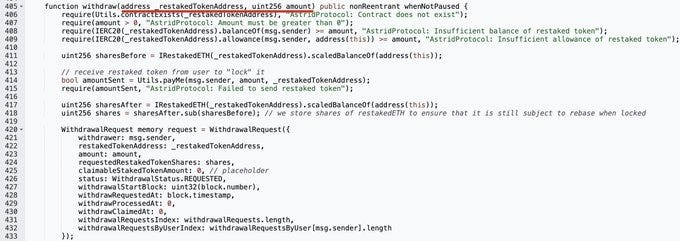
- The root cause of the exploit is due to a vulnerability in the withdraw() function. The flaw allowed attackers to manipulate the arguments for the withdraw function, namely the token address and token amount.
- Attackers created three counterfeit tokens, labelled A, B, and C.
- They utilized fake token A to initiate a withdrawal and obtain stETH.
- Fake token B was used for a withdrawal, resulting in the acquisition of rETH.
- For the third withdrawal, they employed fake token C, enabling them to claim cbETH.
- Subsequently, they converted the acquired stETH, rETH, and cbETH tokens into ETH and gained profits.
Mitigation and Best Practices:
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan
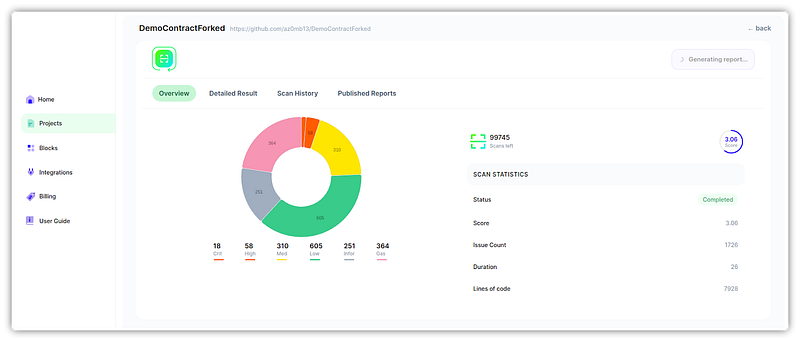
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
