AST Token Hack Analysis
AST Token Hack Analysis
Overview:
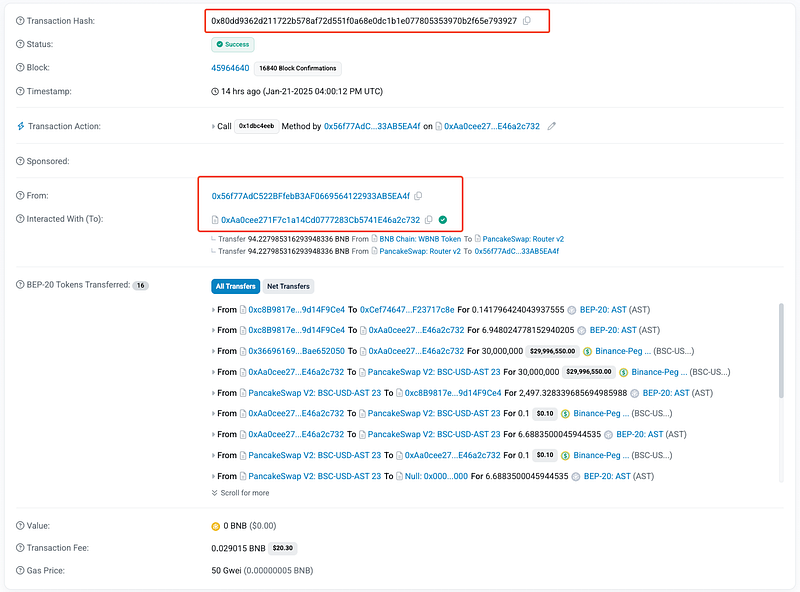
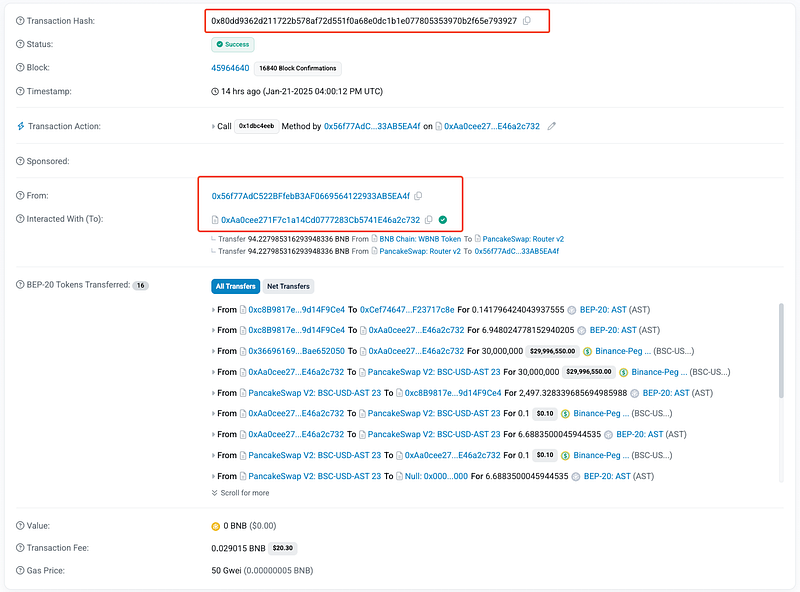
On January 21, 2025, the AST token on the Binance Smart Chain (BSC) was exploited, resulting in a loss of approximately $64.7K in USDT. The vulnerability stemmed from flawed logic in the _transfer function, particularly during liquidity removal scenarios. The attacker exploited this logic to manipulate the AMM reserves on PancakeSwap, allowing them to drain USDT using a small number of AST tokens.
Smart Contract Hack Overview:
Decoding the Smart Contract Vulnerability:
- The root cause lies in the
_transferfunction, specifically in the liquidity removal logic. When liquidity is removed (from == uniswapV2PairandcheckLiquidityRm(to)returns true), the_burn(from, amount)function reduces the pair’s balance but does not increase the user’s (to) balance.
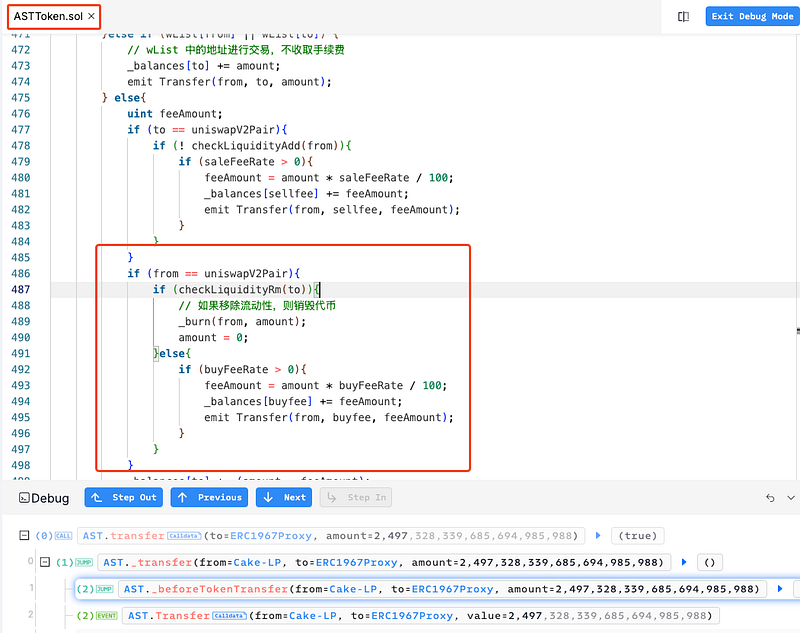
- This results in a double decrease in the pair’s AST balance — once due to liquidity removal and once due to the
_burnfunction. Consequently, the pair is left with an unusually low AST balance. - With an extremely low
x(AST reserve), even a small amount of AST can extract a disproportionate amount of USDT from the pool due to the pricing formula of AMMs:
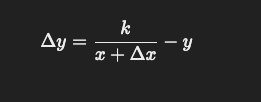
- The imbalance in the reserves (AST and USDT) created by this logic allows the attacker to exploit the AMM’s invariant, enabling them to drain USDT from the pool for minimal AST.
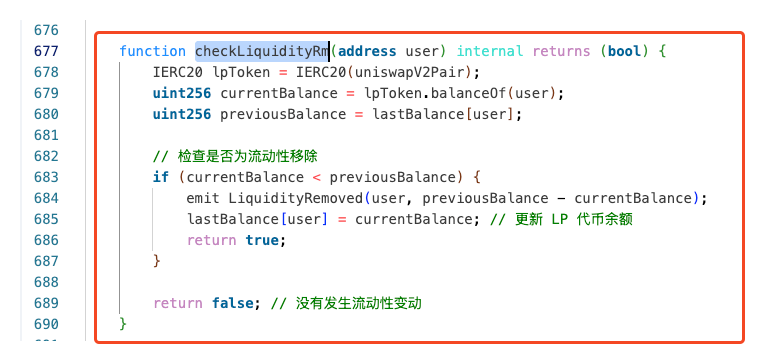
- The function determines if liquidity is being removed by checking the user’s LP token balances (
checkLiquidityRm(to)). However, since the function updateslastBalance[user]only after liquidity removal, the attacker was able to manipulate it for consecutive exploits by transferring a small number of LP tokens to trigger the liquidity removal logic repeatedly.
Attack Flow:
The attacker swapped a large amount of USDT for AST, depleting the pair’s AST reserves to a minimal level.
They transferred a small amount of USDT and AST to the pair and then, aligned the AST balance to a critically low value.
Leveraging the
_transferlogic, the attacker triggered liquidity removal, which further reduced the AST reserves without compensating the pair.
Using the skewed reserves, the attacker repeatedly swapped minimal AST for a disproportionate amount of USDT, draining the pool.
Approximately $64.7K in USDT was stolen and funneled through Tornado Cash.
Mitigation and Best Practices:
- Modify the
_transferfunction to credit the recipient’s balance (to) when liquidity is removed and tokens are burned. This ensures that the pair’s balance is not erroneously reduced twice. - Ensure that liquidity-related logic (e.g., adding/removing liquidity) is carefully handled and validated. This includes ensuring that tokens are not burned unless absolutely necessary.
- Any changes to the liquidity pool should be handled in a way that doesn’t compromise the balance of the token pair.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
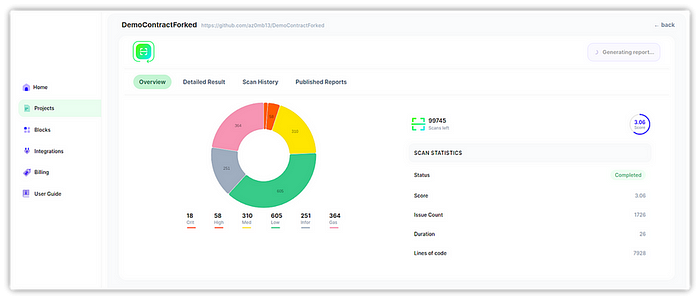
- Scan your Solidity contracts against the latest common security vulnerabilities with 280+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
