Aperture Finance Hack Analysis
Aperture Finance Hack Analysis
Overview:
On January 25, 2026, Aperture Finance (@ApertureFinance) was exploited across multiple chains Ethereum, Arbitrum, and Base resulting in total losses exceeding $3.67 million USD. The root cause in incident was an arbitrary-call vulnerability caused by insufficient input validation, which allowed attackers to abuse existing ERC20 and NFT approvals and drain assets using transferFrom().
The protocol is closed source making the analysis a bit difficult. After decompiling the bytecode and reviewing on-chain execution traces, it became evident that user-controlled parameters were passed into low-level calls without proper constraints. This enabled attackers to redirect execution to token contracts and invoke malicious calls in the context of the victim contracts.
These vulnerabilities fall under OWASP SC Top 10: Arbitrary External Call / Input Validation Failures, a class of issues that becomes especially dangerous when contracts hold broad token approvals.
Smart Contract Hack Overview:
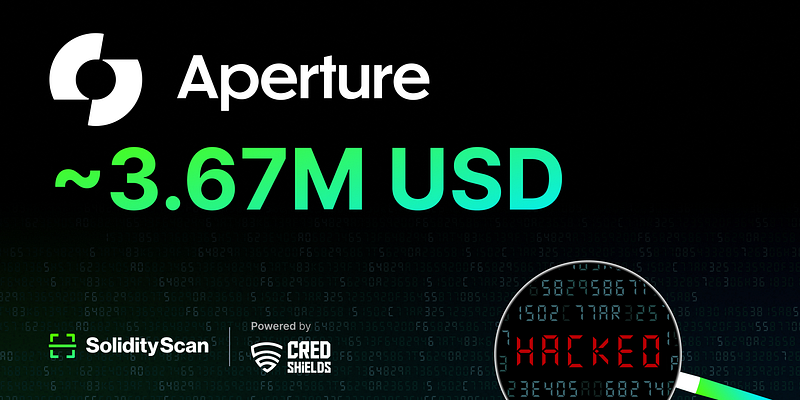
- Attack Transaction:
0x8f28a - Victim Contract:
0xD83d9 - Attacker Addresses:
0xe3e73 - OWASP SC Top 10: SC06:2025 Unchecked External Calls
Decoding the Smart Contract Vulnerability:
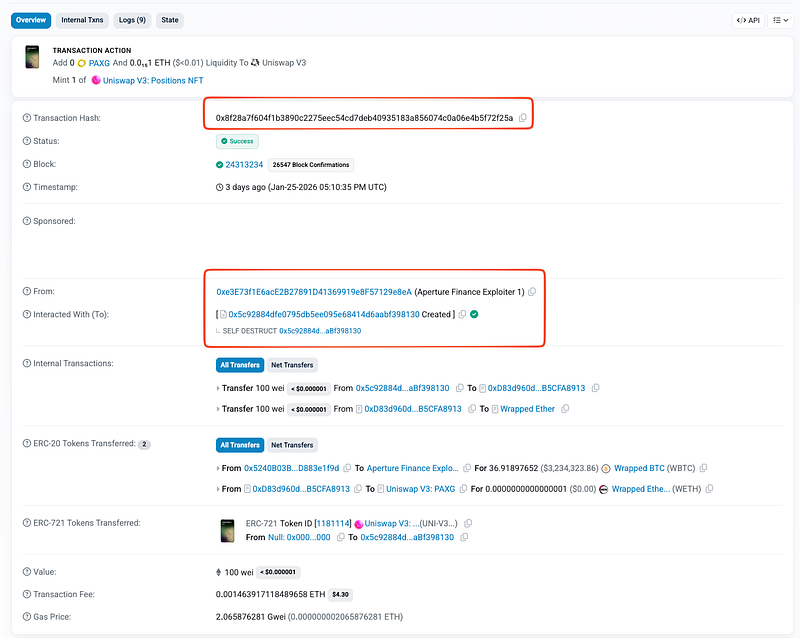
- At the bytecode level the internal swap function
0x1d33()constructs and performs a low-level external call using parameters derived from user input:target(address used incall),calldata(call data / function selector),expectedOutput(value compared against a balance delta later) - The contract did not sufficiently constrain
targetorcalldatato known, safe DEX/router contracts or to an expected function selector. Consequently, an attacker could settargetto any contract (including an ERC-20 token contract) and craftcalldatathat invoked that token’stransferFrom(victim, attacker, amount)(or equivalent). Because the low-level call executes from the victim contract’s context, the token transfer honoured any approvals the victim held, enabling theft.
Two additional enabling factors made the exploit feasible:
- The contract relied on an attacker-controlled
expectedOutputto validate the swap result (balance delta comparison), making that check meaningless when the attacker crafted both the call and the expected result. - The project’s closed-source nature required decompilation to find these specifics, but did not change the attack surface: any low-level call + approvals = risk unless constrained.
Transaction walkthrough
Caller (attacker contract
0x5c92...) calls0x67b34120()on victim.
Victim executes
WETH.deposit()– WETH balance on victim increases by 100 wei.
Victim invokes
0x1d33()with the attacker-provided tuple (target,calldata,expectedOutput).
0x1d33()makes a low-levelcall(target, calldata).
targetis a token contract;calldatamaps totransferFrom(victim, attacker, amount).
transferFromruns in the victim context and moves tokens using prior approval.
0x1d33()checksbalanceAfter - balanceBefore == expectedOutput. The attacker-controlled expectedOutput makes this check trivially pass.
Victim continues and calls
NonfungiblePositionManager.mint(); attacker receives minted position while approved assets are siphoned.
Mitigation and Best Practices:
- Any function that performs
call(target, calldata)must enforcetarget∈ {approved routers/DEXes} and restrictcalldatato a known set of function selectors + ABI formats. If a swap needs flexibility, route everything through trusted adapters/wrappers rather than accepting raw user-controlledtarget/data. - Never validate execution success using user-supplied output deltas; instead compute outcomes from trusted sources (router return values, audited adapters, or balance-change accounting bound to exact input/output tokens). Add hard checks on
tokenIn/tokenOut, minimum amounts, and revert on any unexpected token movement. - Avoid holding broad ERC20 approvals (especially
type(uint256).max) inside operational contracts; use per-swap scoped approvals and reset allowances immediately after use. For user flows, prefer Permit2 / EIP-2612 permits, and add explicit restrictions preventing calls that can triggertransferFrom()on arbitrary tokens or siphon assets via pre-existing approvals. - To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
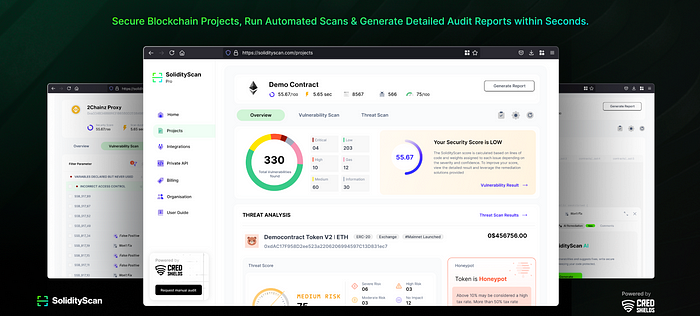
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
