Ankr Hack Analysis
Ankr Hack Analysis
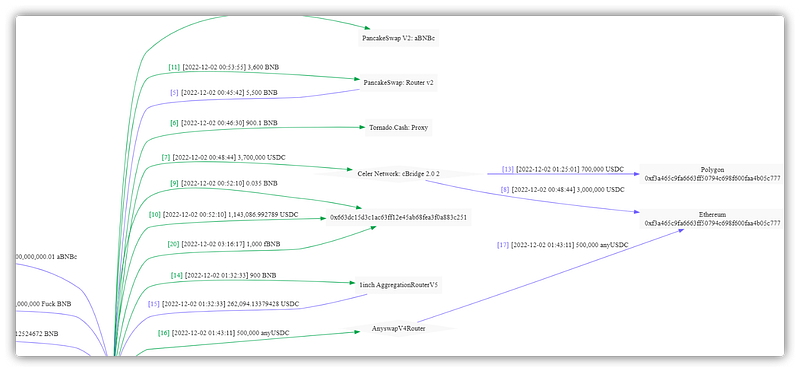
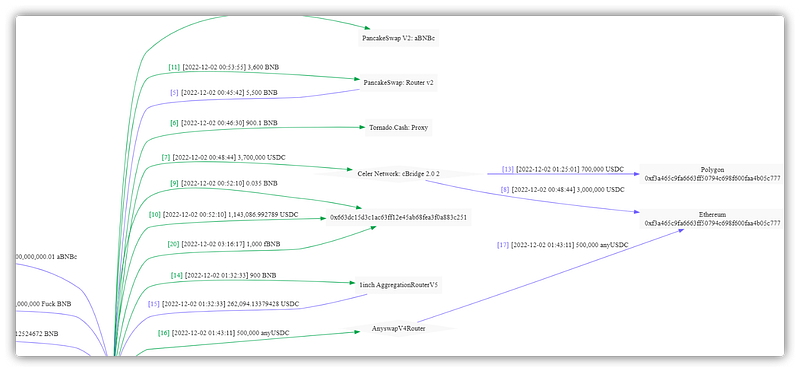
On December 2, 2022, a massive hack occurred that allowed the attacker to mint 6 quadrillion aBNBc tokens from the Ankr on-chain Defi protocol. It was found that a developer’s private key (deployer key) had been compromised, and using the compromised key attacker deployed a malicious contract with a mint function without validation leading to decentralized theft by more than six hundred exploiters worldwide.
Currently, some of the aBNBc that the hacker issued got converted to BNB by pancakeswap, and the remaining amount is kept in the attacker’s wallet. The hacker used Tornado to transfer the stolen funds.
Smart contract hack overview:
- Ankr Staking/proxy Contract Address: 0xE85aFC
- Logic contract address:0xd99955B
- Malicious upgrade tx: 0xcbc5ff4a6c9
- Attackers address: 0xf3a465c9fa
- Attacker’s transaction: 0x61e0f3f0d
- Detail of the attacker’s leftover wallet money: 0xf3a465C9f
- A few addresses used by Ankr exploiters: 0x9ced6f4445f 0x8d11f5b4d
- List of all Ankr’s incident exploiters: spreadsheets/d/1uCBMp
- Recent changes to the logic contract address following the attack: 0x9e6
Decoding the smart contract vulnerability:
- Through the proxy contract 0xE85a, the hacker invoked the logic contract’s 0x3b3a5522 function, which does not validate the authority check and instead issues aBNBc tokens.
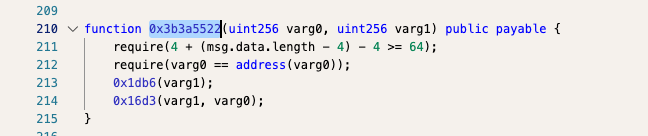
- The proxy contract, further called logic contract 0x16d3 function, was responsible for minting more tokens.
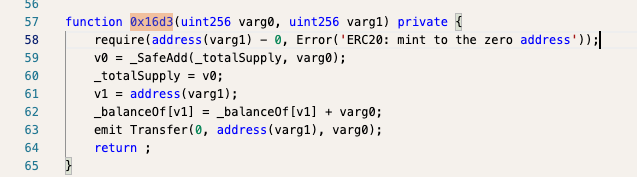
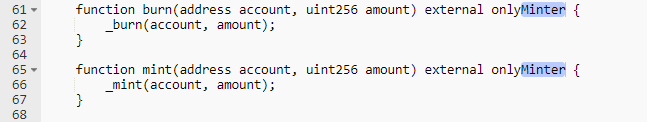
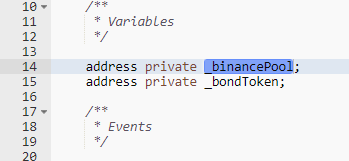
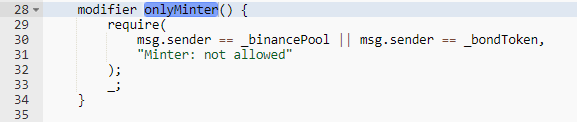
- After being attacked, the project party updated the logic contract once more. In the updated logic contract, the mint function has been checked for permissions, and the
onlyMintermodifier determines whether the sender address is one of the two addresses that can only mint new tokens according to the contract:_binancePoolor_bondToken.
- The fundamental cause of this attack is that when the logic contract’s issued functions make contract upgrades, they do not perform a permission check. As a result, hackers minted more tokens using this vulnerability. More details concerning the attack analysis and the theft of private keys are still being researched, so stay tuned for updates!
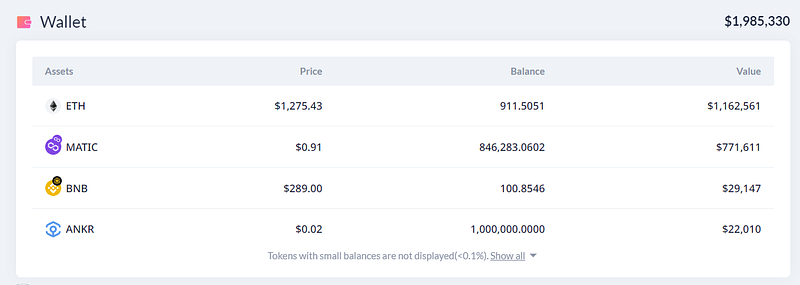
Fig: Wallet of the attacker with pending tokens balance
Mitigation & Best Practices:
- To ensure that only a given address may mint the tokens, sensitive functions like mint should have appropriate access controls like “
onlyMinter” etc. - It is encouraged to utilize libraries from OpenZeppelin to ensure the usage of the “
onlyOwner” qualifier. - To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

