Allbridge Hack Analysis — Improper business logic
Allbridge Hack Analysis — Improper business logic
Overview:
It was reported that on April 1, 2023, a flash loan attack took place on Allbridge’s pool in BSC networks, resulting in a loss of about $570K. The attack happened due to a flawed pricing calculation logic, which caused the attacker to operate in both LP and swapper roles and manipulate the price to drain money.
Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan
Smart Contract Hack Overview:
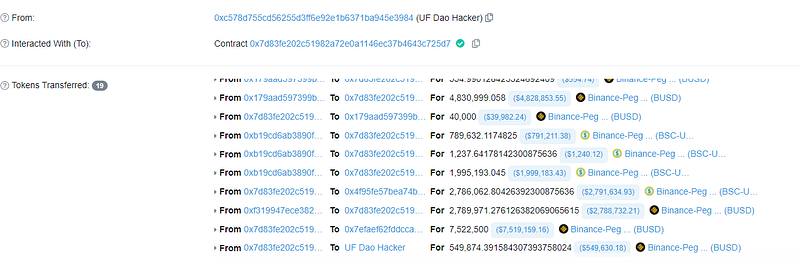
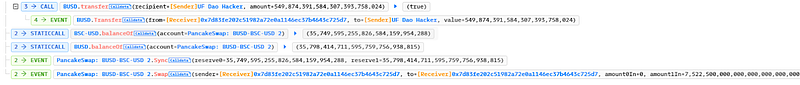
- Attacker’s Address(also UF Dao Hacker): 0x2b3cff12,0xc578d
- Attacker’s Transaction:0x7ff136
- Attacker’s Failed Transaction: 0x18e5f
- Victim pool address: 0x179a,0xb19cd
- AllBridge contract: 0x68784
Decoding the Smart Contract Vulnerability
- The attacker began by getting a flash loan from PancakeSwap for $7.5M BUSD and then swapped $2M BUSD for $2M BSC-USD into the pool. The attacker transferred $5 million BUSD into a different pool and afterward exchanged it for its BSC-USD equivalent.
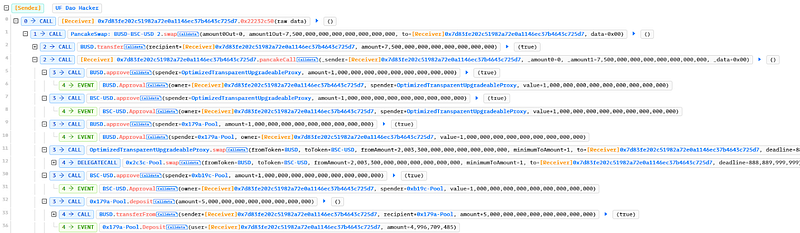
- The attacker now converted the $5M BSC-USD to its $BUSD equivalent and transferred it into Allbridge’s bridge contract, resulting in large profits for the previous liquidity deposits.
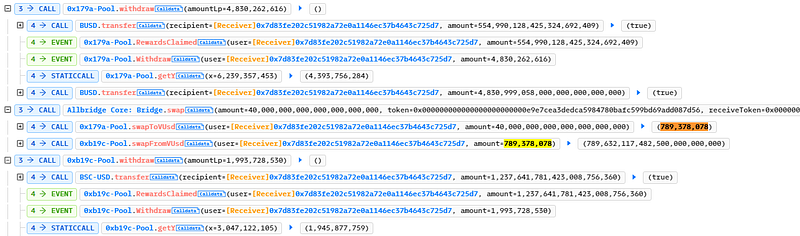
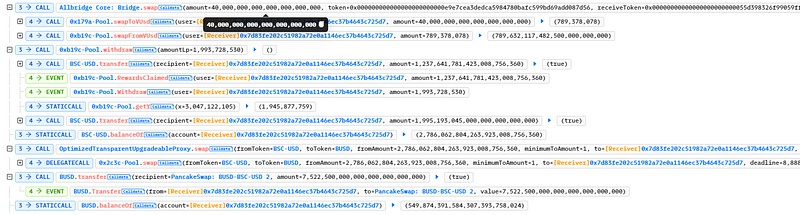
- After the attacker switched the pool balance, the liquidity pool balance was destroyed, and the pool’s balance liquidity was reduced to 40,000 dollars in balance BUSD.
- The attacker then only used $40,000 of BUSD to exchange $790,000 of BSC-USD from Bridge due to broken logic.
- The attacker leveraged tornado cash to transfer $570,000 in BUSD to their wallet address.
Mitigation and Best Practices:
- Always have proper checks on the bridge swap price calculation and do not allow a user to behave as multiple roles in the price calculation business logic for any pool.
- Protocols need to add security layers, using at least two oracles to verify the price. This would mitigate the hack and ensure proper checks on critical functions and variables that are publicly accessible.
- Price manipulation attempts can be mitigated to a greater extent via oracles such as Chain Links and input validation on those feed parameters to prevent stale data.
- Document the system’s access control roles with proper permissions to prevent loss of funds.
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
