Alchemy Cross-Site Scripting Vulnerability
Alchemy Cross-Site Scripting Vulnerability
What is Alchemy?
Alchemy is the most popular web3 development platform. It helps developers to build and scale by instantly connecting your dApp to the blockchain.
On August 20th, 2022, the CredShields team identified a security vulnerability at an endpoint of Alchemy. This blog post will provide an overview of the security vulnerability and the actions taken by the Alchemy team to resolve it.
Sign in with Alchemy Feature:
Alchemy has a feature to allow 3rd party applications to sign in via alchemy. It enables a 3rd party application to obtain limited access to an HTTP service which is either on behalf of a resource owner by orchestrating an approval interaction between the resource owner and the HTTP service or by allowing the 3rd party application to obtain access on its own behalf. It is similar to signing in with google or signing in with Facebook feature, which is quite common in web2.
Let’s understand how it works:
The user clicks on the “Sign in Alchemy” button on a 3rd party website or an application.
- The website or application redirects the user to the Alchemy OAuth endpoint with a request for access to the user’s Alchemy account information.
- The user is prompted to sign in to their Alchemy account if they are not already signed in.
- The user is asked to grant permission for the website or application to access their Alchemy account information.
- Once the user grants permission, Alchemy redirects the user back to the website or application with an authorization code.
- The website or application uses the authorization code to make a request to Alchemy’s token endpoint in order to obtain an access token.
The vulnerability:
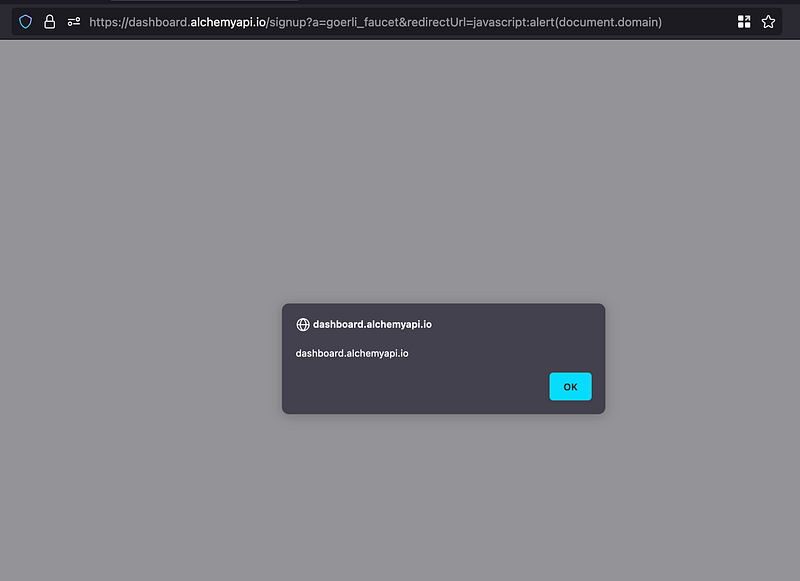
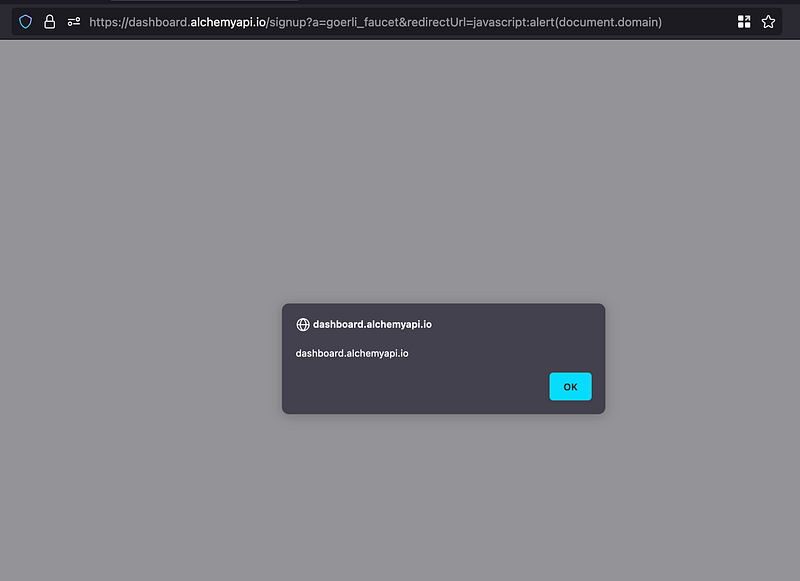
We at CredShields were trying to get some Goreli testnet funds from https://goerlifaucet.com/. We tried authenticating via “Alchemy Login” and noticed the URL below.
https://dashboard.alchemyapi.io/signup?a=goerli_faucet&redirectUrl=https://goerlifaucet.com
Since any form of state verification was missing, we were confident that we could cause a URL redirection. However, an open URL redirection is only a concern if it can be chained with other vulnerabilities. So we looked for input validation, and it was missing. We tried the input value as javascript:alert(document.domain) to execute a cross-site scripting proof of concept, and it worked. Hence we got a cross-site scripting vulnerability in Alchemy.
What is cross-site scripting?
Cross-Site Scripting (XSS) attacks are a type of injection in which malicious scripts are injected into otherwise benign and trusted websites. An attacker can use XSS to send a malicious script to an unsuspecting user. The end user’s browser has no way of knowing that the script should not be trusted and will execute the script. Because it thinks the script came from a trusted source, the malicious script can access any cookies, session tokens, or other sensitive information retained by the browser and used with that site. These scripts can even rewrite the content of the HTML page.
Acknowledgment:
We at the CredShields team are on a mission to make Web3 more secure, so we emailed the Alchemy team. The team found the security issue valid and fixed the vulnerability on 22nd Aug 2022.
About SolidityScan:
The team behind CredShields is building SolidityScan. SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
